Introduction
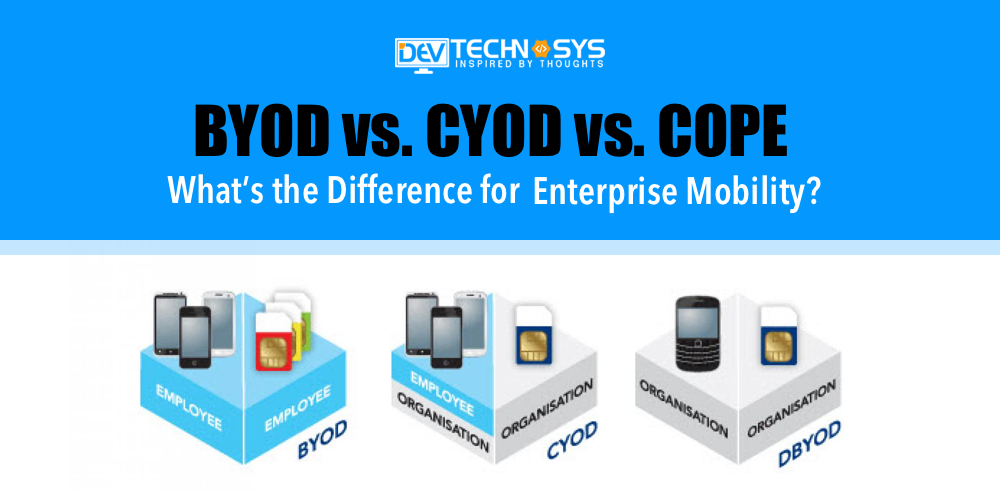
Are you planning to enhance your company’s infrastructure with the addition of enterprise mobility services? You might think to bring different types of mobile devices and begin to use them for your needs. It is not right away to go ahead but. Yes, you need to have a proper plan in place which can define the work which needs to be done to maintain security so that devices and data remain completely secure. There are different options that you can consider in the form of BYOD, COPE, and CYOD. We will further discuss BYOD vs CYOD vs COPE- the difference between them.
Getting the Right Mobility Solutions
If you are confused about the respective options, then you have landed yourself on the best page. Yes, here we are going to discuss BYOD, CYOD, and COPE in detail so that you decide about your need for enterprise mobility solutions with much more clarity. All these modes have their own type of process and rules in play. You will need to understand the different provisions set by the respective modes and then make your decision accordingly.
To make your decision with much clarity one needs to have proper knowledge of the difference between COPE, CYOD, and BYOD. It will help your business avail the right mobile app development solution. We will help you with the key differences you will find in the features of CYOD, BYOD, and COPE so that you can understand which model will fit perfectly for your business needs.
Related Blog: Tips to Enhance Enterprise App Development Process
Exploring the Difference between Modes
Whatever be the model type you select for your business, it is important that you manage and protect the respective devices in the best possible way. This is where enterprise mobility management comes into play with mobile device management. But before this, you need to understand the key differences between the modes, and to help you we have very few of them mentioned below, take a look:
BYOD or Bring Your Own Device
Here we will be discussing the most popular model for your business. Yes, BYOD is one of the highly acknowledged policies for your enterprise mobility solutions. With the help of this policy, employees are allowed to get their devices at the office and use it for their work-related needs. You need to first get the device approved by the respective enterprise and then the application will be installed which will make it easier for you to manage the device security. Yes, there will be no harm to the device from a central management system in the form of an enterprise mobility management solution.
If this model is in usage, the employees will be completely responsible when it comes to keeping the device secure from averting any kind of issues. Yes, you need to prevent it from getting stolen or lost. Not only this, but you also need to make sure that there is no use of public WiFi networks in the respective device. You must also make sure to keep it away from different kinds of malicious applications and programs. It is important so that there are no security-related issues with your device or else it can be difficult for enterprise mobility management solutions to enforce different policies of security.
CYOD or Choose Your Own Device
With the infusion of this policy, you get a pre-approved set of mobile devices with the help of enterprise and give you the opportunity to select one according to your needs. These mobile devices are basically configured with business mobile applications and different security protocols. As per the CYOD policy, the users after selecting the device can own the respective handset by paying for it upfront. You can cover the costs by getting it paid with the stipends and still own the ownership of the device.
When it comes to CYOD, it basically stands in the mid of BYOD and various other modes. This is because it also helps employees with the freedom of getting to select their own devices. In many policies, its enterprise selects the type of device the employees will be getting to use but here it’s up to employees. The enterprises can maintain the compatibility of the device and make sure it is fully security-approved. It will help one have a device and the data which completely safe and secure. So, hopefully, you are clear about what makes CYOD different and why you must go ahead with it!
Related Blog: A Guide to Developing a Successful B2B Web Portal
COPE Or Corporate-Owned, Personally-Enabled
When it comes to COPE, this policy will help users with access to the devices which completely belong to the respective company. Your company will have complete ownership of the respective set of devices and they will be responsible for its operation charges. But with this policy, users also get the freedom to personalize the device as per the specific needs and requirements. Yes, they can have business mobile programs in their device according to their requirements and there will be no objection from the enterprise at all.
Under the COPE policy, enterprises will take complete control of the devices they offer to the users. They will not relinquish the ownership they hold over mobile devices. They can get the devices configured as per their wish and maintain the device security and data of it by infusing the best of mobile programs. These devices are fully protected and the enterprises also have the access to get them locked from beforehand. So, with this policy, users get the least freedom in terms of usage of the device. Not only this, but this policy can also prove to be very expensive when compared with other policies and the reason is because of the ownership changes.
Wrapping Up
So, when it comes to choosing the policy model for your enterprise, it is important that you get a brief idea of it and then make your decision. You can also consider hiring an android developer and understand which policy will work in favor of the business and help you with benefits. Hopefully, you are clear with the differences between CYOD, BYOD, and COPE. So, make your decision and give your business the right platform for mobility solutions.